Key Management Policy Template - General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. This policy and standard apply to. Ensure that reveal consistently follows industry standards for encryption and key management.
Ensure that reveal consistently follows industry standards for encryption and key management. This policy and standard apply to. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption.
Ensure that reveal consistently follows industry standards for encryption and key management. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. This policy and standard apply to.
Encryption Key Management Policy Template
Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. This policy and standard apply to. Ensure that reveal consistently follows industry standards for encryption and key management. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used.
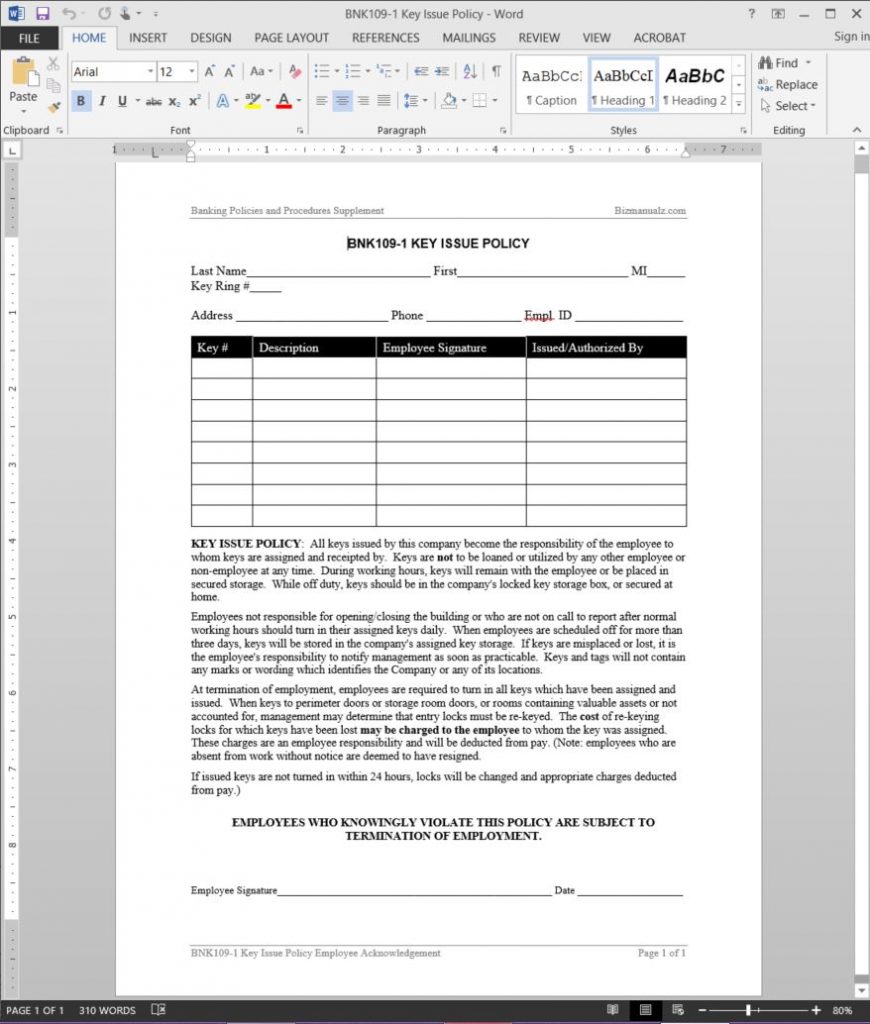
Amazing Key Control Policy Template Policy template, Functional group
Ensure that reveal consistently follows industry standards for encryption and key management. This policy and standard apply to. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used.
Encryption Key Management Policy Template Policy template, Management
Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. This policy and standard apply to. Ensure that reveal consistently follows industry standards for encryption and key management. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used.
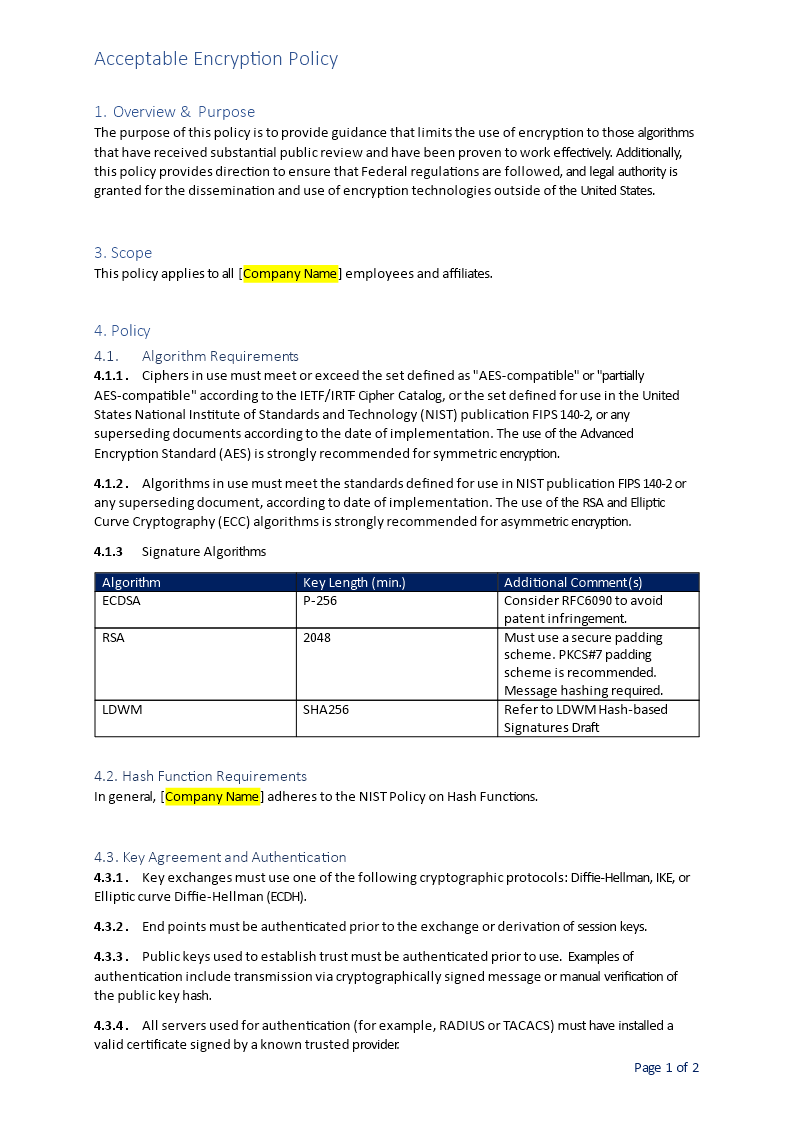
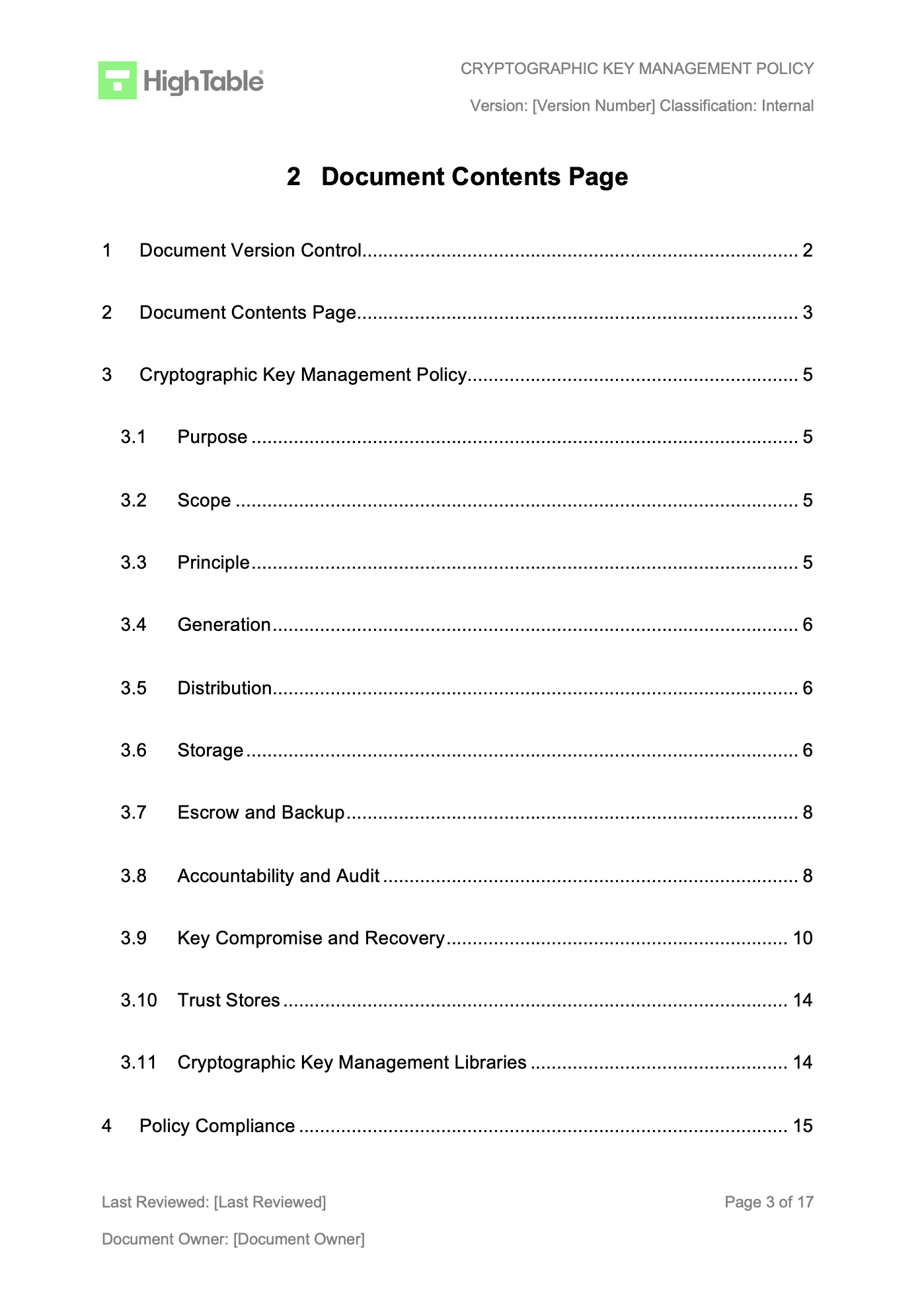
ISO 27001 Cryptographic Key Management Policy Template
Ensure that reveal consistently follows industry standards for encryption and key management. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. This policy and standard apply to.
Fascinating Encryption Key Management Policy Template Sparklingstemware
General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. Ensure that reveal consistently follows industry standards for encryption and key management. This policy and standard apply to. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption.
Amazing Encryption Key Management Policy Template Sparklingstemware
Ensure that reveal consistently follows industry standards for encryption and key management. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. This policy and standard apply to. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption.
ISO 27001 Cryptographic Key Management Policy Template
This policy and standard apply to. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. Ensure that reveal consistently follows industry standards for encryption and key management.
ISO 27001 Cryptographic Key Management Policy Template
This policy and standard apply to. Ensure that reveal consistently follows industry standards for encryption and key management. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used.
ISO 27001 Cryptographic Key Management Policy Template
Ensure that reveal consistently follows industry standards for encryption and key management. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. This policy and standard apply to.
Key Management Policy Template
This policy and standard apply to. Ensure that reveal consistently follows industry standards for encryption and key management. Cio 2100.1, “gsa information technology (it) security policy.” when used to protect sensitive information, federal systems must use encryption. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used.
Cio 2100.1, “Gsa Information Technology (It) Security Policy.” When Used To Protect Sensitive Information, Federal Systems Must Use Encryption.
This policy and standard apply to. Ensure that reveal consistently follows industry standards for encryption and key management. General requirements for the key management process must be defined to ensure appropriate secure management of cryptographic keys used.